In the previous post, a new Copilot was published on the site.
2024.10.05 - [Copilot Studio] - Copilot Studio. Deploying Copilot to an IIS Site.
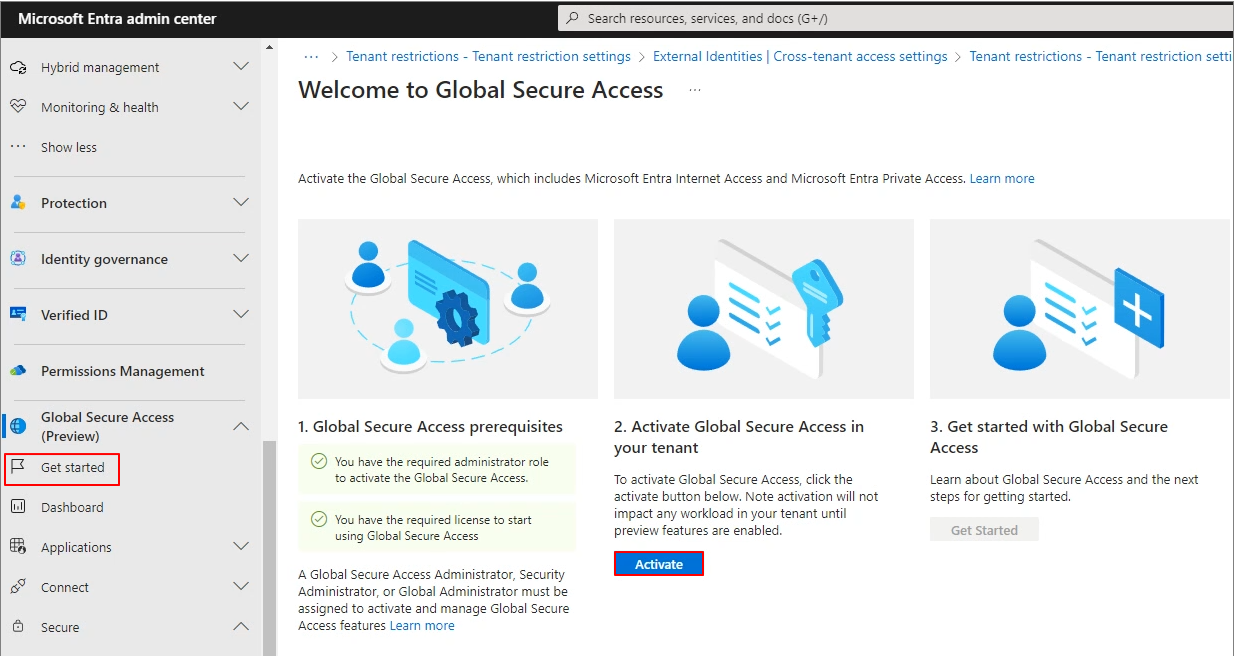
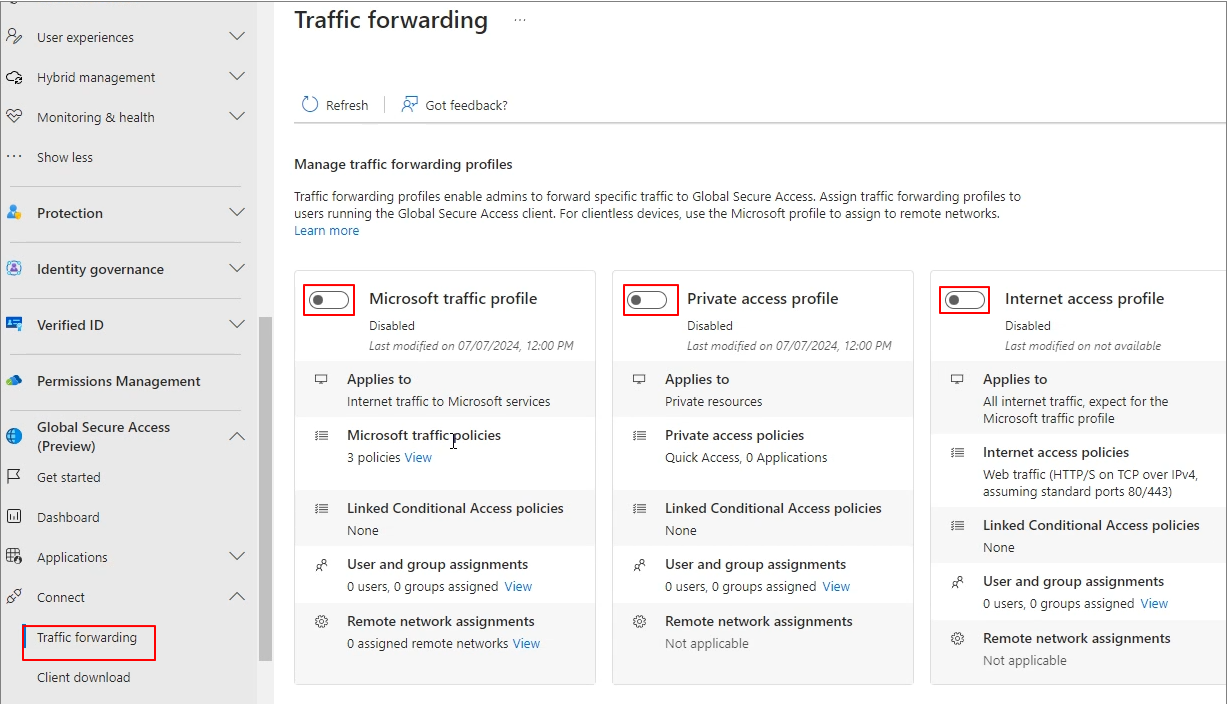
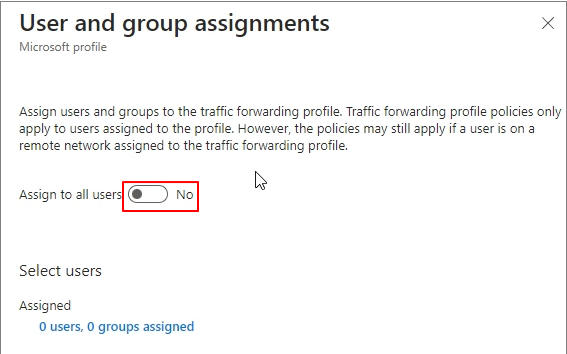
This time, I have written about how to configure Entra ID and SSO in cases where the organization requires that only authenticated users have access.
The following technical documentation was used as a reference.
Configure user authentication with Microsoft Entra ID - Microsoft Copilot Studio | Microsoft Learn
Configure single sign-on with Microsoft Entra ID - Microsoft Copilot Studio | Microsoft Learn
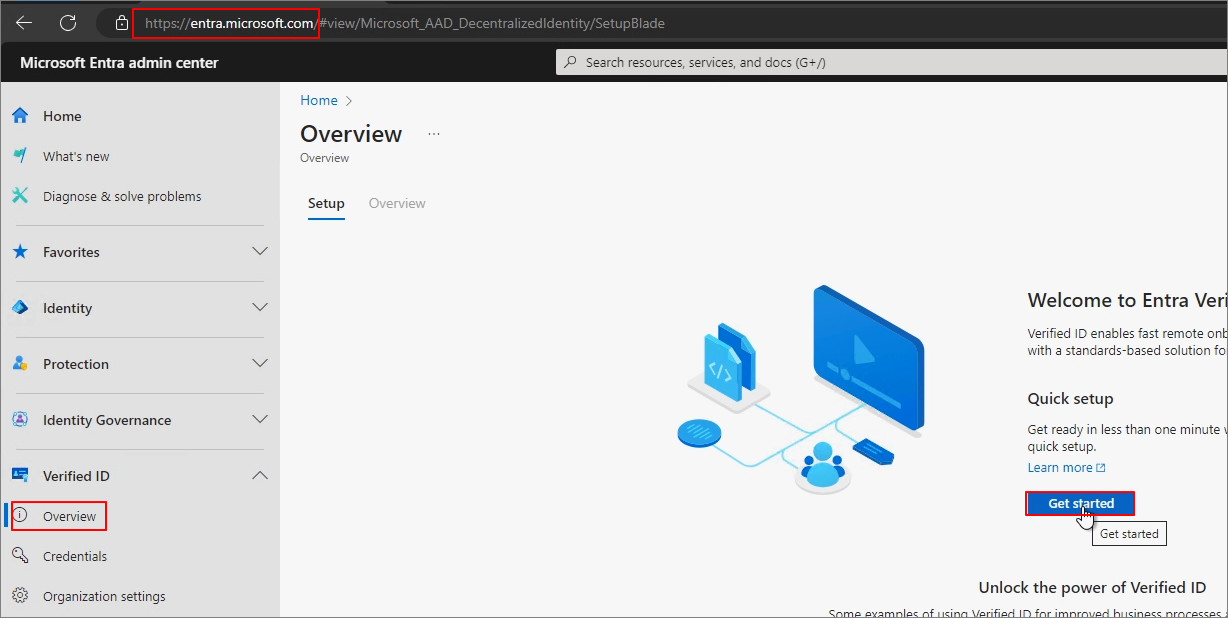
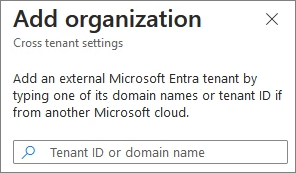
Entra Admin Center -> Applications -> App registrations -> New registration

After entering the App name, click Register (At this stage, the Redirect URI is optional. The URL below was created based on my test page.).

Navigate to Authentication.
Add the following URL mentioned in the technical documentation.
https://token.botframework.com/.auth/web/redirect
https://europe.token.botframework.com/.auth/web/redirect
Check Access tokens and ID Tokens -> Click Save.

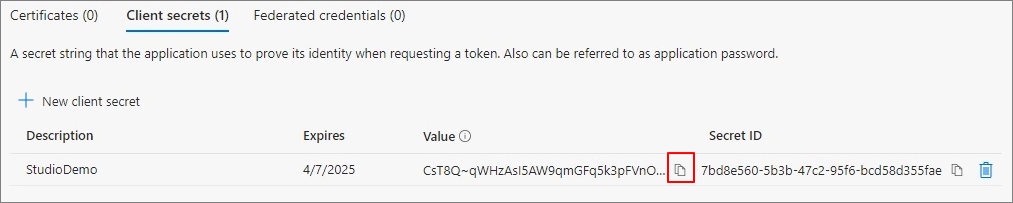
Certificates & secrets -> Client secrets -> New client secret

Input Description -> Add
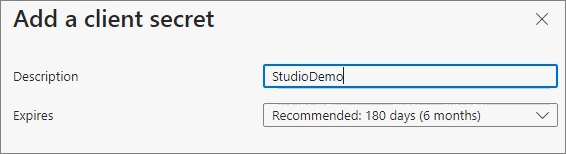
Save the Value in advance.
Go to Overview and save the Application ID information.

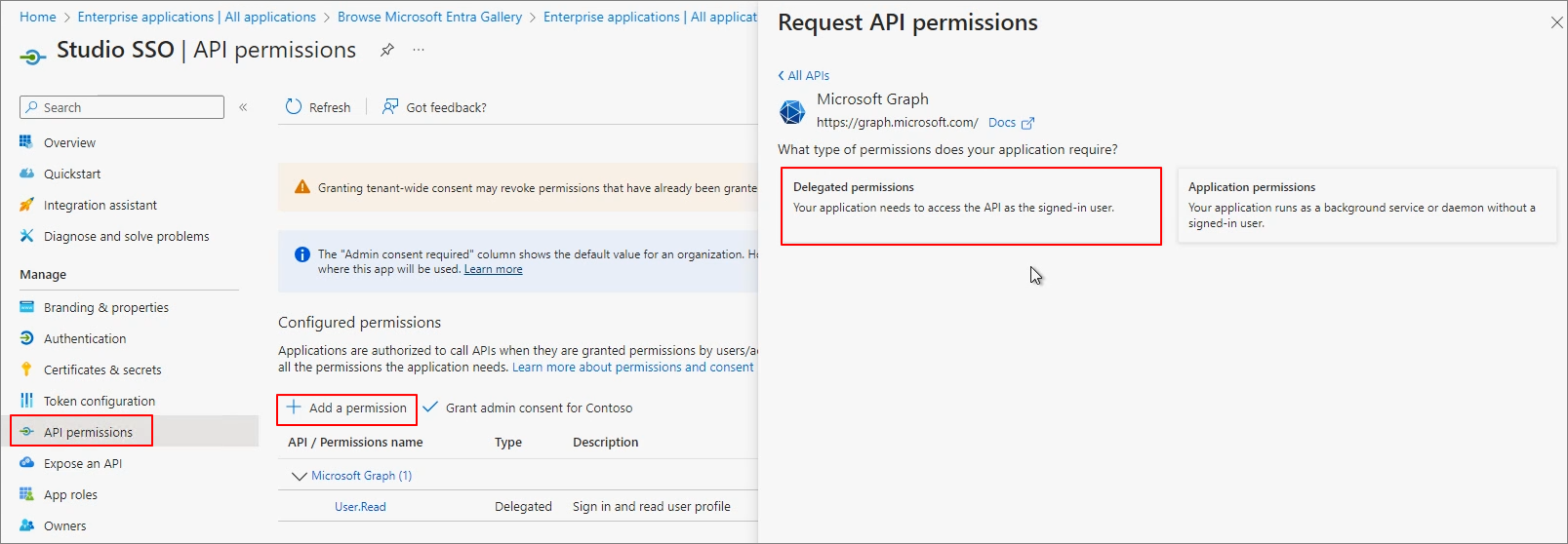
API permissions -> Add a permission -> Delegated permissions
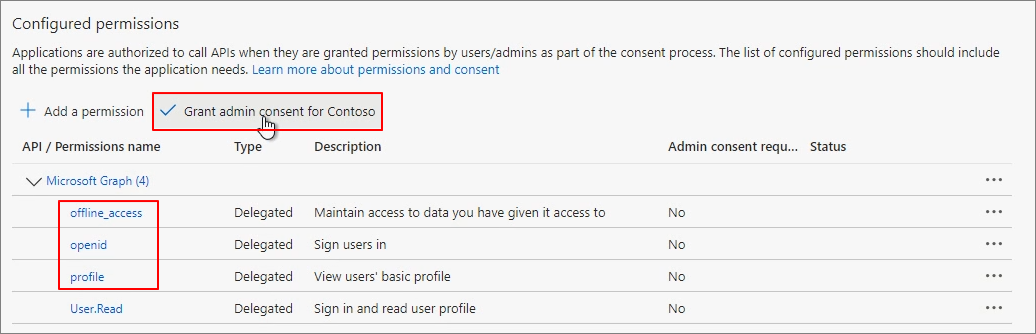
Add the permissions offline_access, openid, and profile. -> Grant admin consent for Contoso
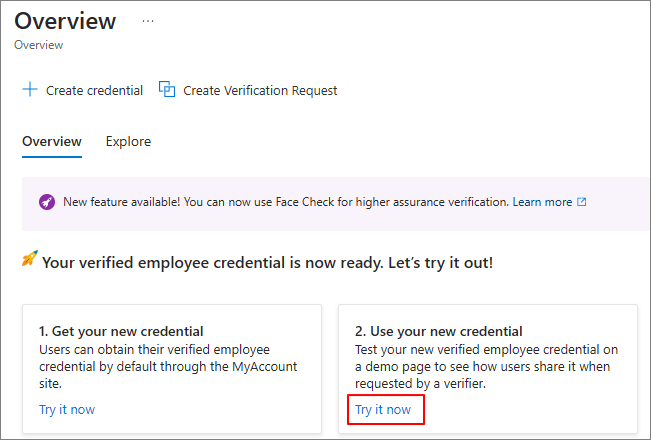
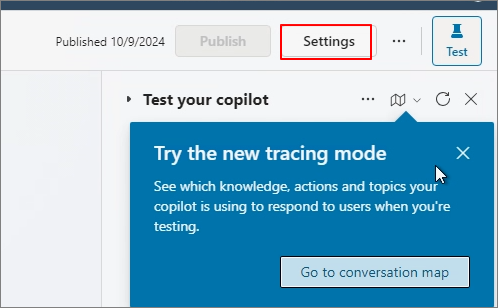
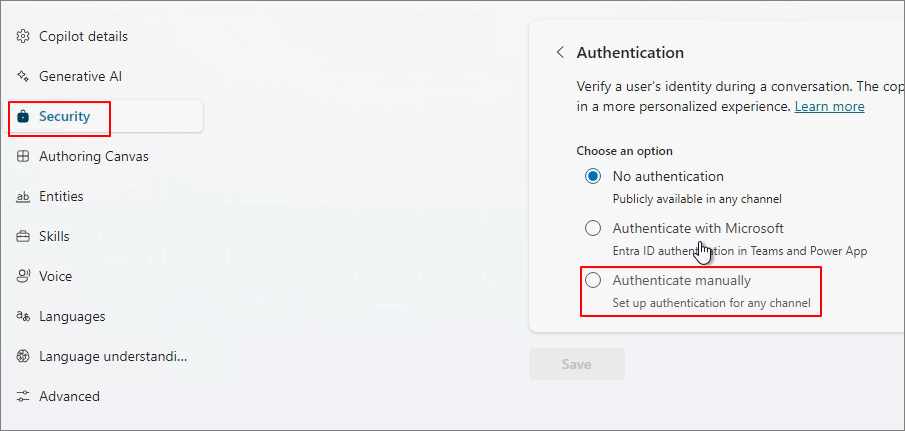
Go to Copilot Studio and navigate to the Settings menu of the Custom Copilot you want to modify the authentication for.
Security -> Authentication -> Authenticate manually
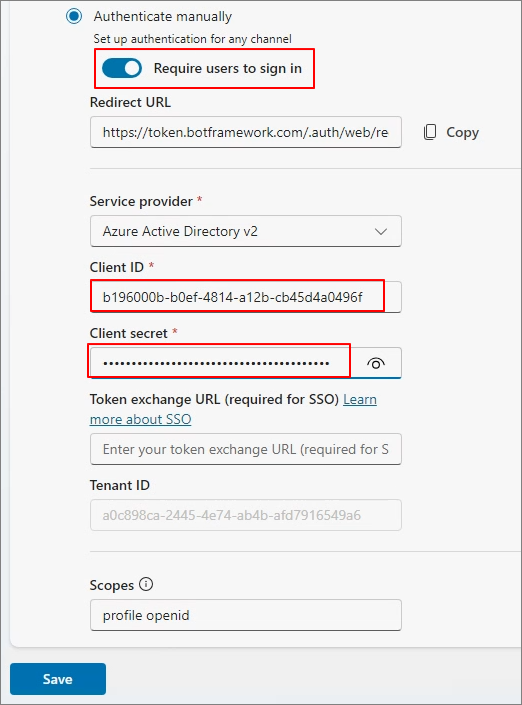
Select Require users to sign in -> Enter Client ID (App ID) and Client secret (Value) -> Click Save -> Click Publish.
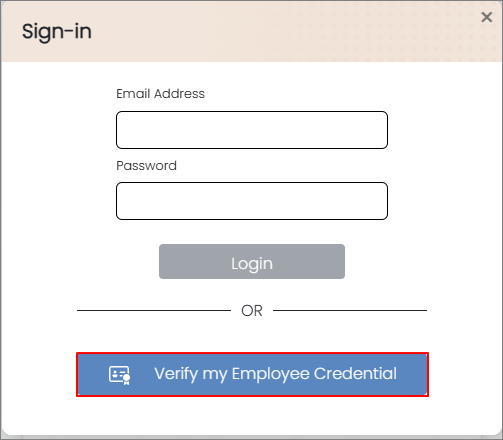
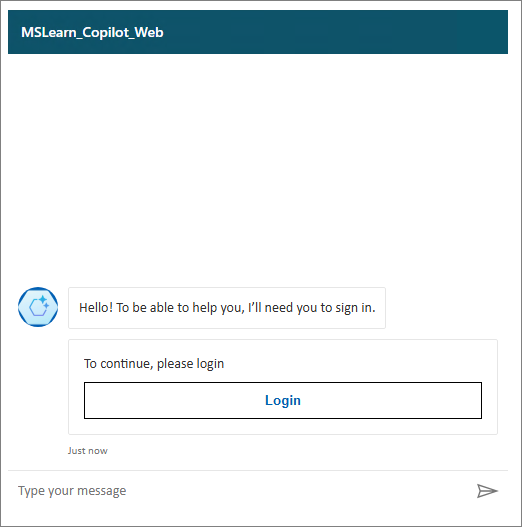
A message indicating that a login is required will appear as shown below.
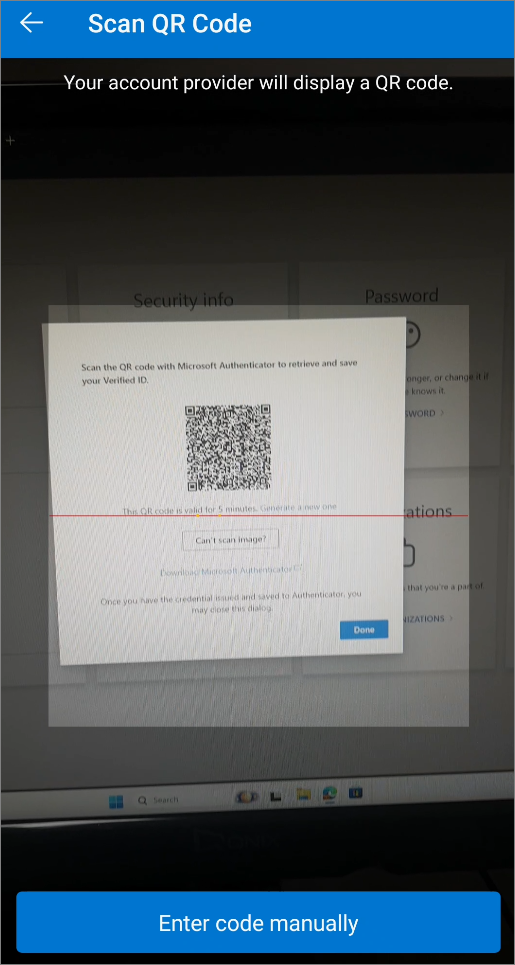
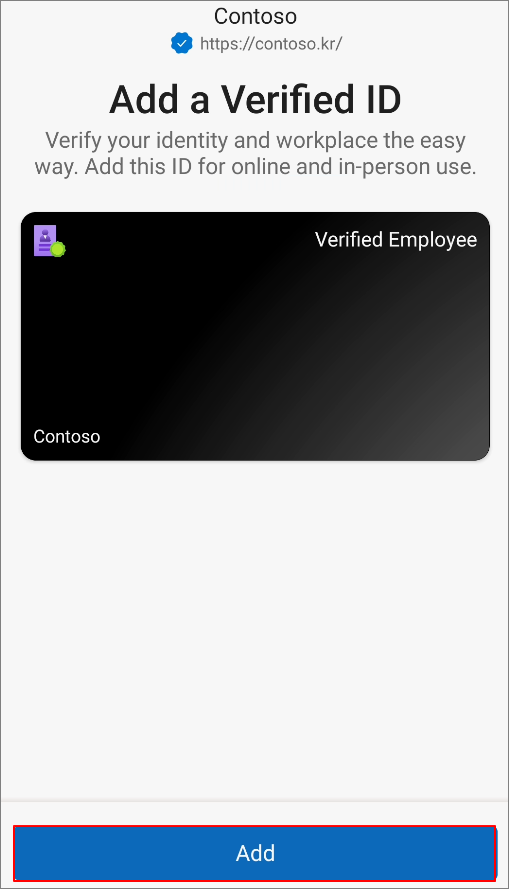
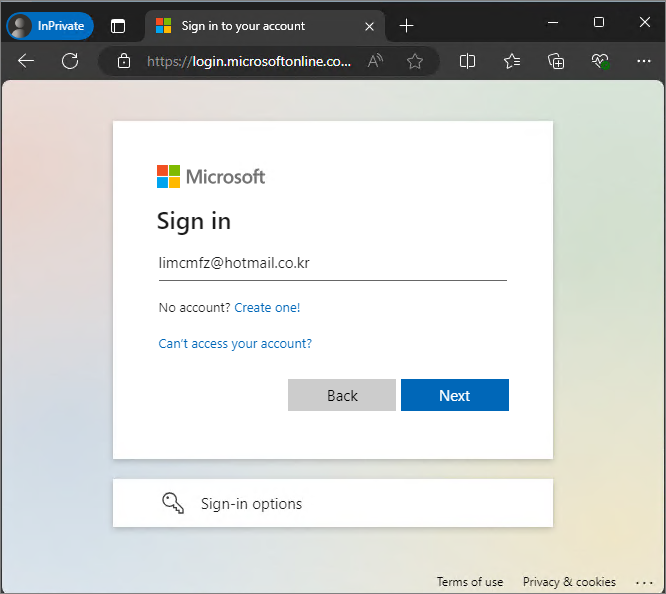
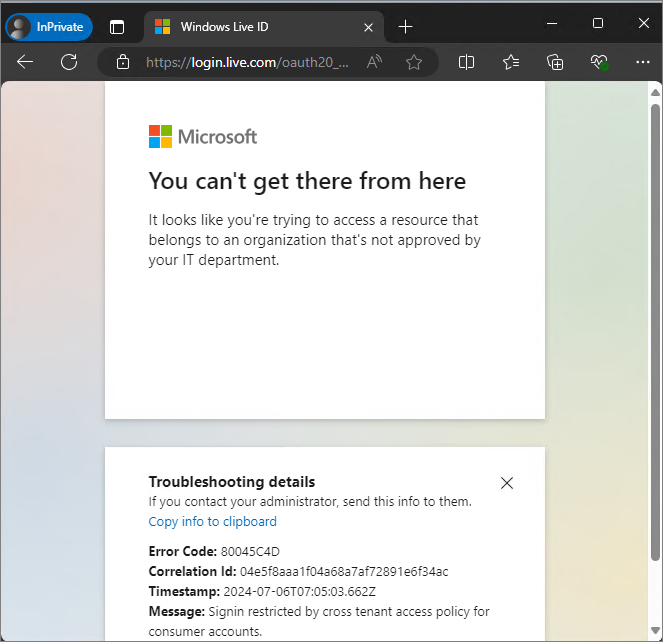
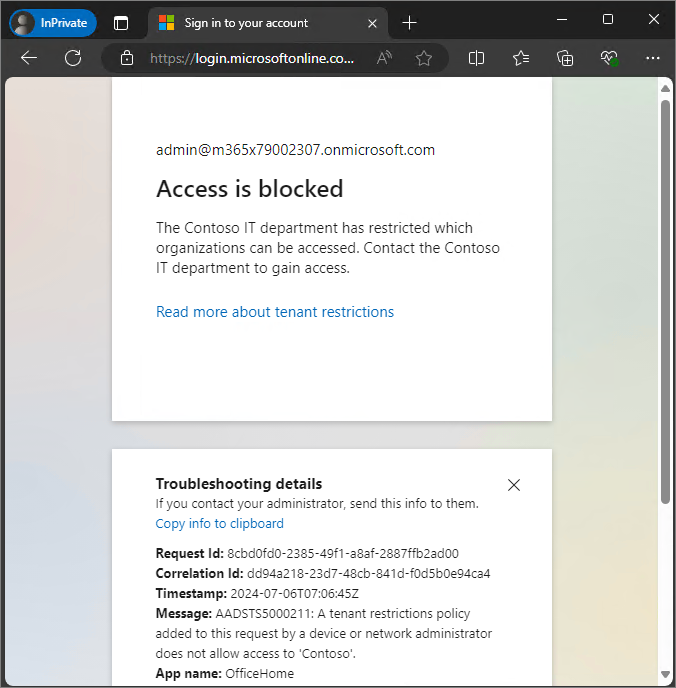
Access the Copilot web page in a separate browser -> Click Login -> Complete the Login process.
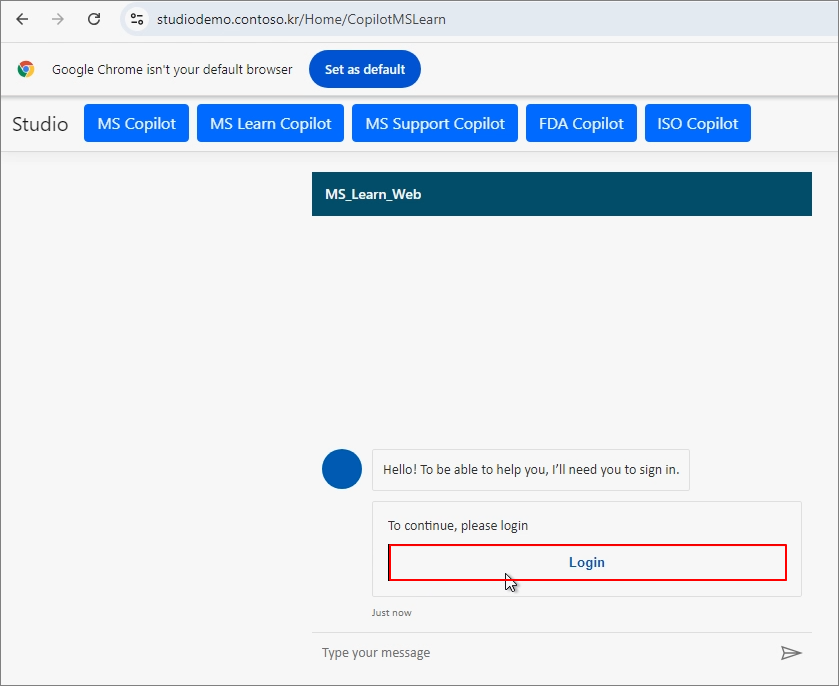
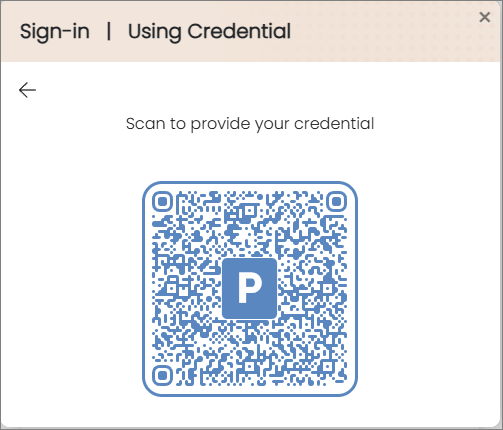
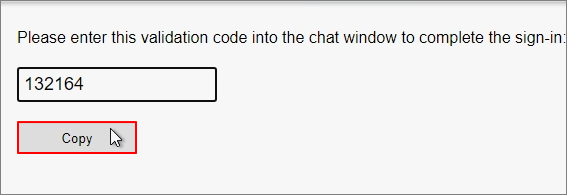
Copy the Validation Code provided after logging in.
Enter a message in the chat window to confirm that the authentication was successful.
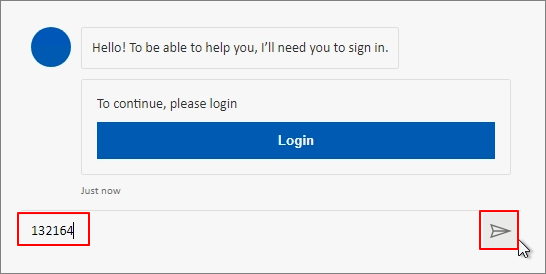
Since login cannot be implemented directly in the chat, it seems that the authentication process is carried out using a separate validation code.
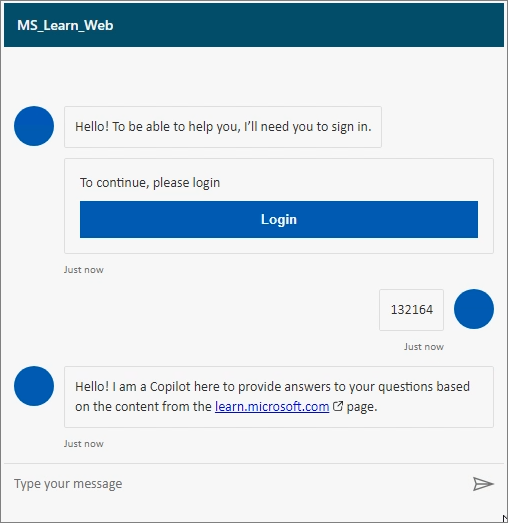
By configuring it this way, you can set up security so that only users with an account can access the Custom Copilot.